
Did you know that Samsung is the world leader in digital technologies, particularly for the greatest number of mobile phones sold in 2021? About 112.5 million units were sold to end-users by the company in the first two quarters. So, it’s no wonder that the younger generation uses Samsung phones to socialize all day and night.
Although mobile technologies have brought comfort into people’s lives, these devices have become a source of serious danger, too. Cyberbullies, secret death groups, dangerous challenges, and online predators — these are problems thousands of people face on the Internet.
Table Of Contents
Why and How to Track a Samsung Phone of Your Kid
As was noted above, anyone can get into trouble even when they’re in the room next door to you. Online predators use Tinder, Snapchat, Kik, and other apps to get to their victims. And this is an even greater risk for the younger generation.
In most cases, maniacs don’t even need to pretend to be teenagers — kids willingly communicate with all kinds of people, regardless of age. It could even get worse.
Sexting with strangers and sending intimate content has become a pretty common thing today. The fun stops when predators show their true faces and start manipulating kids to send more naked photos and videos. Very often, the online explosion turns physical, as predators can pressure teens to meet up in reality.
You should to be aware of what’s happening in your loved one’s life, both real and digital. If your child is depressed but tells you nothing, this is a tell-tale sign that they’re being harassed by someone.
Pressuring a person to answer your questions can make a situation even worse. That’s why you need an alternative way to find out the truth, such as monitoring your kid’s online activity and tracking their locations.
Can You Track a Samsung Phone?
You can have your own reasons to track your loved ones. And when it comes to their safety, you might want to keep an eye on them while you’re not around. Luckily, there are many ways to do this these days.
If your loved ones are Samsung users, the task even easier for you. Samsung has a built-in feature that can easily find their location in no time. In this article, you can find 4 proven ways to locate your kid’s Samsung phone and prevent them from getting into trouble. Keep on reading to find out more.
1. How to Track a Samsung Phone Remotely with mSpy
Wanna know how to find the location of a Samsung phone? You should consider using a parental control app, such as mSpy. This is the best way to track someone. mSpy will easily locate your kid’s phone remotely right from your smartphone.
With this app, you can also set geofencing if you worry about them visiting unwanted places. And do so much more than this.
Depending on the mSpy subscription type, you can get access to a number of useful monitoring features, such as:
- Monitoring incoming and outgoing calls
- Viewing received, sent, and deleted text messages
- Monitoring Snapchat, Facebook, Tinder, Kik, and other apps
- Looking through sent and received media files
- Viewing browsing history and bookmarks
- Seeing events in a calendar and notes
Only a few simple steps are needed to start monitoring your kid’s phone:
- Go to mSpy.com and pick a subscription.
- Create an account with your relevant email address.
- Follow the installation instructions sent to your email.
- Log in to your mSpy Control Panel and add the monitored device.
- Start monitoring.
If you have questions about mSpy installation and using the app, feel free to contact our support team. And if you need help with installing the app remotely, consider buying mAssistance.
2. How to Track a Samsung Phone Remotely With Scannero
Is there an even simpler way to find your child’s phone and learn his location? Luckily, there is, so you may want to try Scannero. It’s a powerful tool that will let you see where your loved ones are in just a few steps. What makes this one stand out is that it’ll take no more than just two minutes!
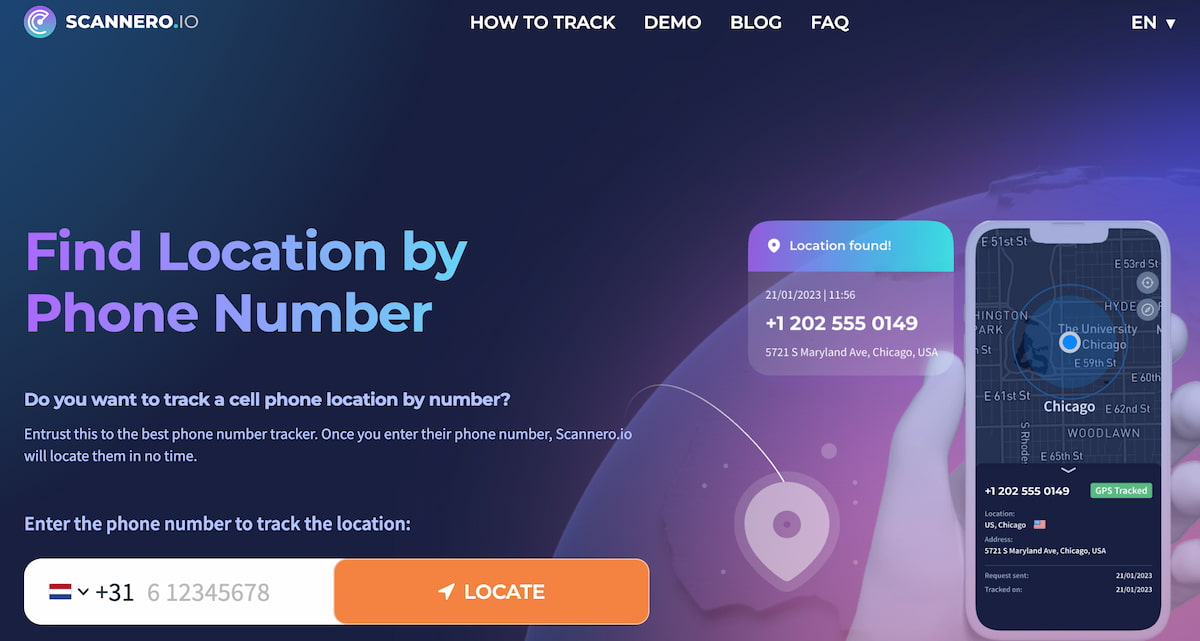
Scannero is a phone tracker by number capable of tracking any phone’s location by its number, as this service works with any and all mobile network providers.
What’s more, there’s no need to install any additional apps neither on your nor your child’s phone. Let’s see how simple it is. Here’s how it works step by step:
- Create an account and purchase a subscription.
- Type in your loved one’s phone number.
- Customize the message with a location-sharing request or leave it as it is.
- Scannero will send this message to their phone.
- Wait for them to open the text message and agree to be located.
- Get a message with your loved one’s location.
Looking for a more feature-rich solution to track a Samsung Phone remotely? Then you should give a parental control app, such as mSpy, a try and start feeling even more secure as a parent.
3. Find My Mobile for Samsung
If your loved one owns a Samsung and you need to find their location, you can use a special service for Samsung users. Find My Mobile helps to locate a phone and secure the data in case the device is stolen. What’s more, you can use the service to unlock the phone remotely.
Before using the service, make sure that the data backup feature is activated on the target Samsung device. If you’re not sure whether it’s turned on, access their phone, go to Settings, tap Lock Screen and Security, and click Find My Mobile. Sign in, if needed, and turn on all the features you see on the screen.
When you need to locate your kid’s Samsung phone, follow these steps:
- Open your browser and go to Find My Mobile website.
- Sign in to their Samsung account.
- Select the needed device from the list.
- Wait until the system loads the phone’s current location. If nothing happens, it means the phone is turned off.
- If the phone is on, you can see the location information and the battery level.
In addition to finding your loved one’s location, Find My Mobile allows you to lock and unlock the device remotely, erase and back up the data, and retrieve calls and messages. The list of available interactions depends on your kid’s Samsung phone model.
4. Find My Device for Android
Although the majority of smartphone users use Samsung phones operated on Android, there are cases when a device runs on another OS. If you want to track a Samsung by using the Find My Device service, keep in mind that it works only for Android devices.
To start tracking a Samsung phone using this method, follow these steps:
- Open your browser and go to Find My Device page.
- Log in to a target user’s Google account or type in the email and password used to register the monitored phone.
- Choose the needed device from the list.
- Start tracking the location.
Keep in mind that a target Samsung phone should be turned on. Otherwise, you won’t see any location information.
5. How to Track a Samsung Location With an iPhone
If you still think that it’s hard to track a Samsung phone using iPhone, you’re wrong. And we’re going to prove it. All you need is Google maps which can be a great alternative to other Samsung phone trackers. More importantly, it’s free. So, here’s a guide on how to find someone’s location on a Samsung phone:
- Install the Google Maps app on your loved one’siPhone.
- Open Google Maps and tap a profile picture in the top-right corner.
- Then go to the Location Sharing tab.
- Set a sharing time, and then choose yourself in a contact list.
- Decide how you want to share the location (email, personal text or social media messages).
- Follow the link in the message to view your loved one’s location.
This method is easy-to-use and it works perfectly when you need to find someone quickly. But as you might know, it doesn’t go beyond GPS tracking. So if you’re searching for more than this, you should consider getting a monitoring app like mSpy.
Conclusion
As you see, there are 4 reliable and legal ways to monitor your kid’s device. Using these methods, you can also find your Galaxy phone in case it’s lost or stolen. However, if you want a bunch of handy monitoring features in your parenting arsenal, we recommend using mSpy.
As mSpy works in stealth mode, your loved ones are unlikely to detect it. And even if they do, you’ll know right away and can easily reinstall it.





I want tracking my wife mobile
Good morning can I be able to track the phone history movements around January 2021.can I be able to track it via dates and time?
Hello, Justice! Sadly, with a monitoring app, you’ll only be able to track the device’s location that the owner went to after the app was installed on the phone. You can only look up past location history on the device itself through Google Maps.