

If you seek a monitoring app to check out someone else’s online activity, you’re likely to face a challenge. There are hundreds of monitoring apps on the Internet, but only a few of them are worth your attention.
For instance, you can run into InterGuard — a monitoring solution that’s packed with a variety of features. However, the app is designed for corporate use. So, it can be pretty difficult for individual users to set up the app.
As an option, you can the mSpy parental control app that is easy to use and simple to install.
Table Of Contents
What Is InterGuard?
InterGard is a monitoring app that makes it possible to check out another person’s online activity remotely. It tracks their mobile phone, tablet, and PC activity and transfers it right to the supervising person’s account.
The developer claims that the InterGuard software rests on three pillars: record, report, and alert.
InterGuard records everything ever performed on a target device. It means you can see someone else’s data, such as emails, social media chats, iMessages, browsing history, and locations.
You can set customized reports when using InterGuard or pick from 30 ready-made patterns. Any of them can run by default at a chosen time. If you monitor multiple people, you can rank them according to the frequency of their performed routines (such as sending emails or browsing sites).
The app provides a well-tailored alert system. It can identify an unordinary activity, such as frequent file downloading, printing, or emailing. What’s more, it allows creating alerts for using websites and keywords by a target person.
How Does InterGuard Work?
Getting started with InterGuard is simple. Just follow these steps:
- Create an account on interguardsoftware.com.
- Buy a subscription. You can choose a license right away or get a Free Trial to make sure the app suits you well.
- Download the app. Remote deployment is accessible for ten and more licenses.
- Log in to your user dashboard and start monitoring another person’s activity.
Note that it’s impossible to deliver the recorded data to your account without an Internet connection at least once a day.
No rooting or jailbreaking is required if a device runs Android 2.1+ or iOS 8.0+. If it has an earlier Android or iOS version, rooting and jailbreaking are a must. Note that after rooting or jailbreaking, a target device won’t get updates from Google and Apple.
How Much Does InterGuard Cost?
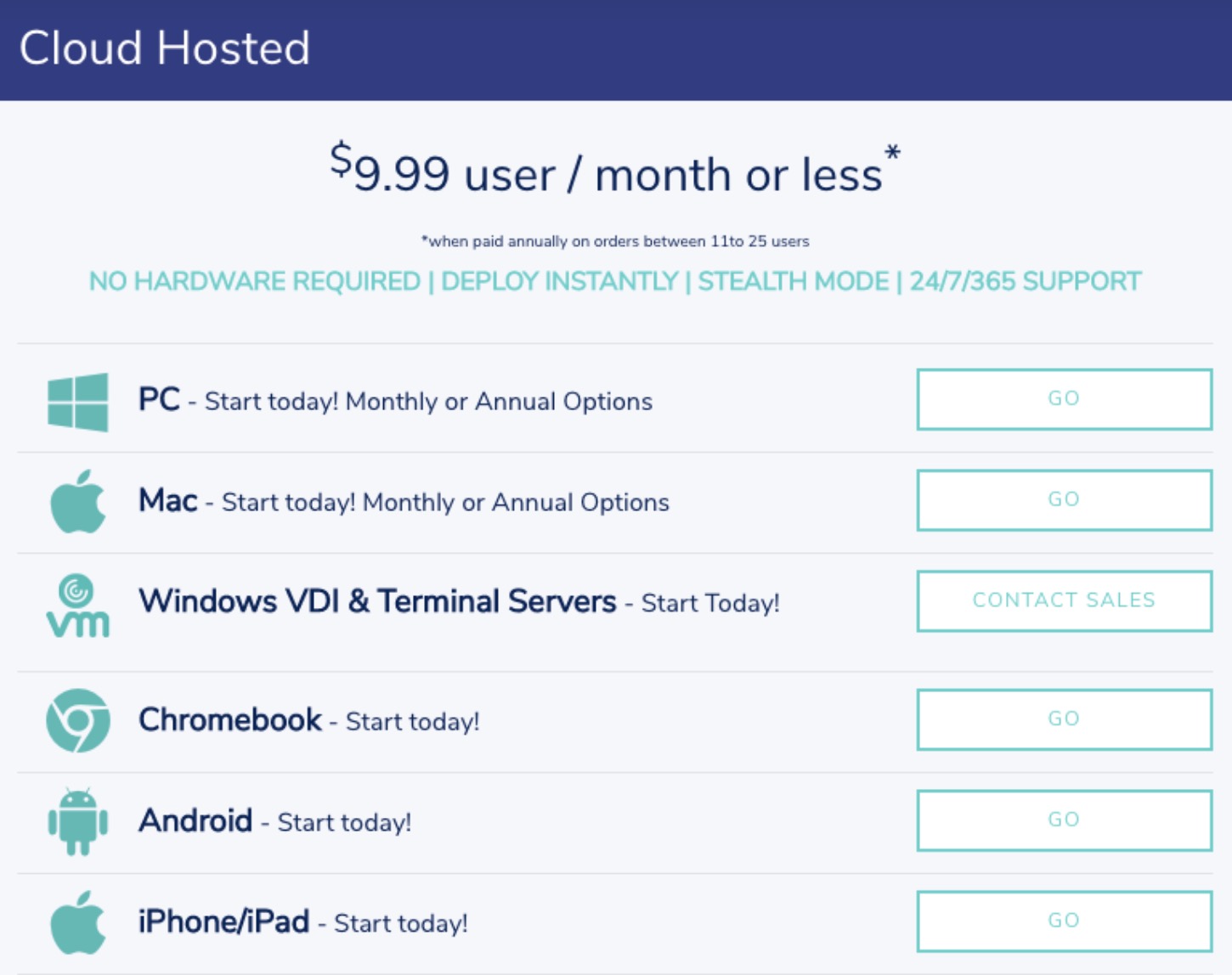
You can purchase the cloud-hosted InterGuard services for $9.99 per user per month. By the way, the app will cost you less money if you buy their annual subscription.
If you need to purchase the app for an organization, you can contact the InterGuard sales managers for details on their On-Premises and Enterprise plans.
You’re welcome to purchase InterGard using Visa, MasterCard, American Express, Discover, PayPal, Check, or Money Order.
What Features Does InterGuard Support?
Social Media Monitoring
InterGuard can easily monitor someone else’s use of social media during set hours. It allows you to check out how much time a target person spends on social media, what social sites they visit, and what they send to others.
Monitor their LinkedIn, WhatsApp, Facebook, and Twitter right from your dashboard.
Time Tracker
InterGuard makes it possible to track work performance on another person’s device. You can monitor their log-in and log-out sessions, check activity rates, take optional screenshots, and track GPS locations. The feature perfectly suits measuring someone else’s productivity.
Smart Alerting
InterGuard allows setting alerts for predefined activities and acting on those alerts. You can get notifications right to your user dashboard or set the recipients who will receive alerts by email. The alert subject can vary — starting from data theft alerts and ending with notifications about suspicious chatting.
The app can send you three types of alerts: keyword alerts with screenshots, policy violation alerts, and alerts on suspicious behavior.
Email Monitoring
InterGuard can record all email attachment activity of a target person. It allows you to monitor their sent and received emails and also check out deleted ones. The app will notify you about unusual behavior, such as overusing an email service or sending a huge number of attachments.
You can customize email monitoring according to your needs. For instance, you can choose to opt out of monitoring particular email accounts or teams.
Online Activity and Browsing History
You can check out what sites a monitored person visits and create a list of allowed ones. The system will notify you if a monitored person visits a forbidden site. What’s more, you can see the list of visited sites and search queries.
If you disapprove of visiting particular web pages, you can block them by categories, keywords, or URLs.
You’re welcome to customize the feature by setting web activity monitoring by groups, departments, or individual users.
Keylogging
Whenever you need to capture someone else’s keystrokes, InterGuard can help you. It allows intercepting what a target person types in their browser, chat, emails, and offline documents.
The Keylogger by InterGuard keeps an eye on all keystrokes on a monitored device and sends you real-time alerts if any suspicious behavior is detected.
File Activity
If a target person is responsible for transferring important files, you can check their performance remotely. You can track all their file activity, such as emailing, copying, deleting, editing, downloading, and uploading any sensitive documents.
You can gain full insight into those activities, get real-time alerts on suspicious file behaviors, and block access to selected files and folders.
mSpy vs InterGuard: Corporate Software or Parental App?
As you can discover from InterGuard reviews, the app was created to meet the needs of businesses and corporations. It covers many features, but most of them are more suited for companies rather than individuals.
If you need to monitor a single person, we recommend trying a parental control app, such as mSpy. It also covers a broad range of monitoring functionality and is designed to let you watch another person remotely.
Here are some other reasons to pick mSpy:
- An easy-to-use app designed for everyday people who don’t have strong technical skills;
- Accurate data that updates regularly;
- Flexible pricing policy and variety of payment options;
- More than 30 monitoring features that give you a clear picture of someone else’s online activity;
- Basic features that don’t require rooting or jailbreaking a target device;
- Customer support is available 24/7.
In a nutshell, the mSpy app is an excellent alternative to InterGuard and other monitoring apps. mSpy takes care of keeping your data safe and helps you to find out what another person is up to online.



